Partially Radiation-Tolerant OBC Architectures for LEO Missions: A Cost-Optimized Reliability Approach
- February 6, 2026
- CAVU Aerospace UK
In Low Earth Orbit (LEO), where satellites typically operate at altitudes of about 400–800 km, electronic systems are continuously exposed to radiation originating from solar activity and trapped particles around the Earth. This environment can lead to transient malfunctions, unexpected system resets, or even permanent damage to onboard electronics. Since the On-Board Computer (OBC) serves as the central control unit (responsible for data processing, subsystem management, mission software execution, and communication with ground stations) radiation protection has long been a critical design challenge in spacecraft engineering.
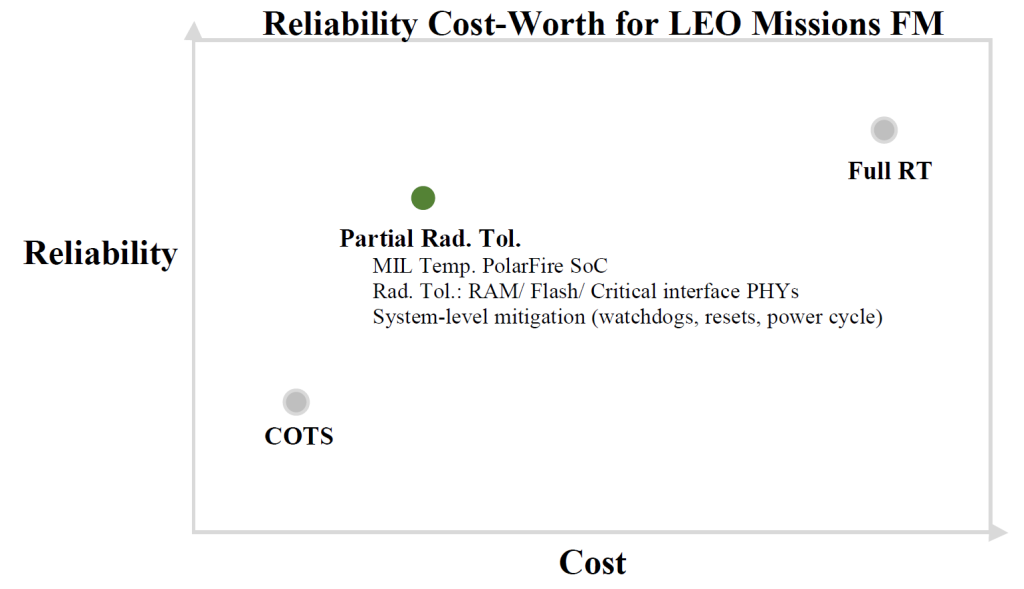
While fully radiation-hardened OBCs are engineered to withstand Total Ionizing Dose (TID) levels exceeding 100 krad and Single Event Effects (SEE) up to LET ≥ 60 MeV·cm²/mg, they typically come with major cost and schedule penalties, often costing 8–10× more than alternative solutions and requiring lead times of 12–24 months. For many LEO missions with durations of 2–7 years, this level of protection is unnecessary. This gap has driven the adoption of partially radiation-tolerant OBC architectures, which strategically balance reliability, cost, and development time. In this article, we will explain in detail what these architectures are, why they are particularly well suited for LEO missions, and how intelligent component selection can deliver high flight-model reliability without excessive cost.
LEO Radiation Environment and System Design Requirements
Typical LEO radiation exposure, assuming 4–6 mm of aluminum shielding, results in:
- TID levels of approximately 5–20 krad over a 5-year mission, depending on orbital inclination and solar activity
- Proton-induced Single Event Effects as the dominant radiation risk
- Heavy ion flux significantly lower than GEO or interplanetary environments
Under these conditions, full radiation-hard margins are often unnecessary. Instead, compliance with ECSS-Q-ST-60-15C, ECSS-E-ST-10-04, and NASA EEE-INST-002 guidelines can be achieved through selective component hardening and system-level mitigation techniques.
Reliability Focused OBC Component Selection Strategy
Improving OBC reliability without incurring a major cost increase requires a structured systems engineering approach. A comprehensive Failure Modes and Effects Analysis (FMEA) is essential to identify failure paths that could lead to loss of mission or loss of spacecraft. The resulting Critical Item List (CIL) highlights components where radiation-induced failures have the highest operational impact.
Experience across multiple LEO programs shows that the most critical contributors to unrecoverable radiation events in OBCs typically include:
- Volatile memory (SEUs, SEL-induced corruption)
- Non-volatile memory (SEFI events, stuck bits, accelerated wear-out)
- Power management ICs (single-event latch-up and single-event burnout)
- High-speed interface PHYs (link loss or permanent degradation)

Selective Integration of Radiation Tolerant Components
A highly cost-effective mitigation strategy is to selectively upgrade only these high-impact components to radiation-tolerant alternatives with specifications such as:
Radiation-Tolerant SRAM / DDR
- TID tolerance of ≥ 30–50 krad(Si)
- SEL immunity up to LET ≥ 60 MeV·cm²/mg
- SEU rates compatible with ECC-based mitigation schemes
Radiation-Tolerant Flash / MRAM
- TID tolerance of ≥ 50 krad(Si)
- Reduced susceptibility to SEFI events
- Improved data retention under proton exposure
Radiation-Tolerant Power Regulators and Supervisors
- SEL-free operation up to LET ≥ 60 MeV·cm²/mg
- SEB-hardened MOSFET structures
- Stable output during transient radiation events
Radiation-Tolerant Interface PHYs (CAN, SpaceWire, Ethernet)
- TID tolerance of ≥ 30 krad(Si)
- Reduced risk of latch-up or permanent link failure
These targeted upgrades dramatically reduce the probability of unrecoverable faults while introducing only a modest cost increase compared to fully radiation-hardened OBC solutions.

OBC Polar Architecture for Cost Efficient LEO Missions
The OBC-Polar platform is based on the Microchip PolarFire FPGA SoC, which provides inherent radiation robustness well suited for LEO missions:
- Latch-up immune by design due to flash-based FPGA fabric
- Heavy-ion SEE performance demonstrated up to LET ≈ 37 MeV·cm²/mg
- Typical TID tolerance in the range of 25–50 krad(Si), depending on device selection and mission profile
For many LEO missions, this level of radiation performance already meets or exceeds system requirements. Replacing the PolarFire SoC with a fully rad-hard processor would introduce a substantial cost increase with only marginal reliability gains within the LEO radiation envelope.
A more balanced and cost-optimized approach is therefore to retain the PolarFire SoC while selectively upgrading surrounding subsystems—memory devices, power regulation, and critical interface ICs—to radiation-tolerant versions. This strategy improves overall system reliability, reduces the likelihood of SEL-induced power cycling or permanent memory corruption, and minimizes mission risk without disproportionate cost penalties.

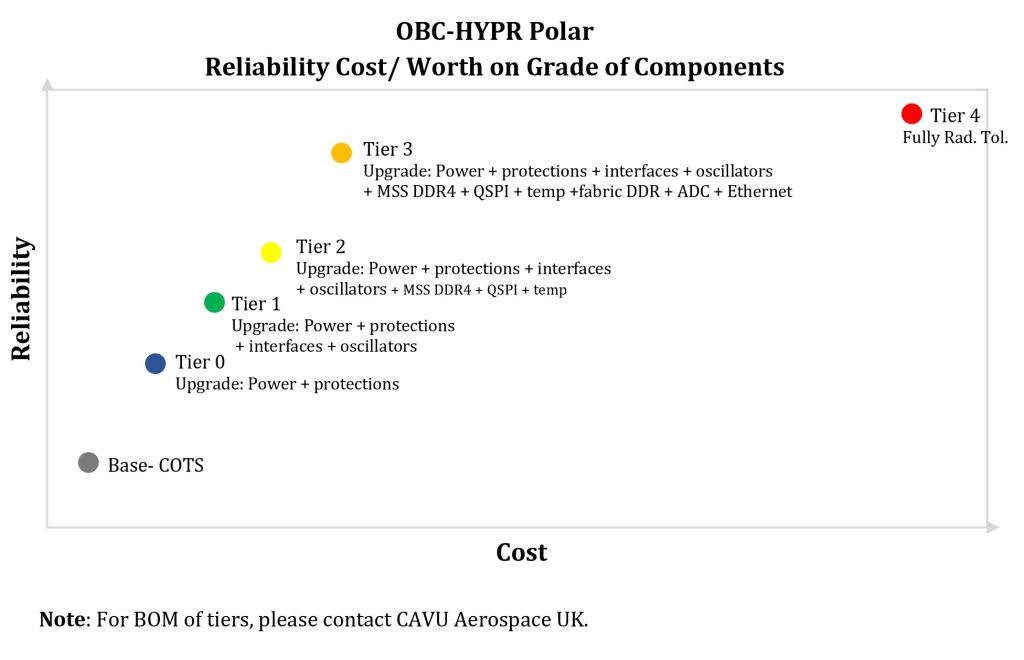
Cost Effective OBC Reliability Strategy for LEO Flight Models
For many LEO flight models, partially radiation-tolerant OBC architectures provide the optimal balance between reliability, cost, and schedule. By applying FMEA- and CIL-driven design decisions and selectively hardening only the most critical subsystems, robust FM performance can be achieved while remaining fully aligned with ECSS and NASA standards.
This value-for-money approach avoids the excessive cost and long lead times associated with fully rad-hard designs, while still enabling reliable spacecraft operations.
Recommended OBC Architecture for LEO Flight Models
- Retain the standard or military-temperature PolarFire SoC (MIL temperature offering slightly increased cost)
- Upgrade RAM, Flash, power supplies, and critical interface PHYs to radiation-tolerant variants where beneficial
- Rely on proven system-level mitigation techniques, including watchdogs, resets, and controlled power cycling